Top Cybersecurity Trends to Watch in 2026
March 3, 2026

Cyber risk in 2026 is more aggressive, more automated, and more disruptive than ever. Hackers are leveraging artificial intelligence, exploiting third-party vendors, and refining ransomware tactics that can halt corporate operations in hours.
Understanding where threats are headed this year allows companies to act before an incident forces the issue. Learn some cybersecurity basics in our corporate guide, Cybersecurity Costs: Why Protection is Cheaper Than Recovery
AI-Driven Attacks Accelerate Risk
Artificial intelligence has changed both sides of the cybersecurity equation. Attackers use AI to scan for vulnerabilities, generate convincing phishing messages, and adapt malware in real time to avoid detection. This results in faster breaches and shorter response windows. Many of these techniques are visible in modern phishing campaigns, including those explored in Phishing 2.0: How AI Made Cyber Attacks Smarter, More Dangerous.
Continuous monitoring, behavioral analysis, and clearly defined response processes are now baseline requirements for every company regardless of size or location.
Deepfake-Enabled Fraud Grows
Deepfake technology has moved beyond novelty. In 2026, it's being used to impersonate executives, manipulate financial transactions, and exploit employee trust. A convincing voice message or video call can bypass informal approval processes and pressure employees into transferring funds or sharing sensitive data. Strong identity controls, out-of-band verification, and employee cybersecurity awareness training are critical safeguards as social engineering tactics become more difficult to detect.
Learn more in the STACK Cybersecurity Deepfake Detection Guide.
Shadow AI Increases Data Exposure
Employees across industries are using AI tools without formal approval or guidance. This Shadow AI usage creates unmonitored data paths for internal documents, customer information, and intellectual property. Behavioral research highlighted in the Oh Behave! report sponsored by the National Cybersecurity Alliance shows many workers admit to sharing sensitive information with AI tools without employer knowledge.
When policies are unclear, employees default to speed. That behavior turns productivity tools into data leakage risks.
Supply Chain and Third-Party Risk
Your security posture is only as strong as your weakest vendor. Cybercriminals increasingly target third-party providers to gain indirect access to larger companies. This risk is especially acute for manufacturers and defense suppliers, as outlined in Safeguarding Manufacturing Operations Against Cyber Threats.
Regulatory pressure continues to rise. Defense contractors face increasing enforcement as discussed in CMMC Cybersecurity Deadline Approaches for Pentagon Contractors.
Zero Trust Principles Gain Traction
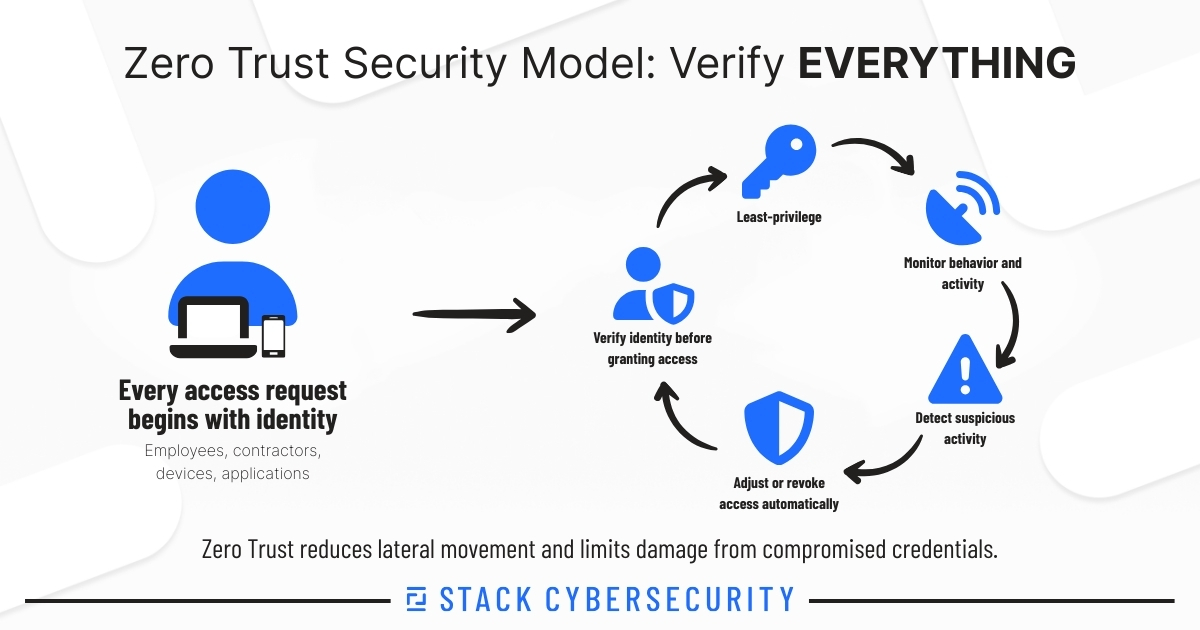
Zero Trust is built on a simple principle: never assume trust. Every user, device, and connection must be verified before access is granted.
This approach reduces lateral movement inside networks and limits damage when credentials are compromised. Identity controls, least-privilege access, and continuous monitoring strengthen resilience.
As insurers and regulators scrutinize security posture more closely, zero trust-aligned controls increasingly influence cyber insurance outcomes.
Cyber Insurance Scrutiny Intensifies
Cyber insurance remains an important risk-transfer tool, but coverage and payouts aren't guaranteed. Insurers now closely examine security controls, training practices, and policy enforcement after incidents.
As explained in How to Prepare for Your Cyber Insurance Journey, misalignment between stated controls and actual practices can result in denied claims.
Governance, ROI
Cybersecurity decisions increasingly sit with executive leadership. Governance, risk, and compliance frameworks connect technical controls to accountability and business outcomes.
STACK’s perspective on this shift is detailed in Cyber GRC: Why Governance Matters.
The financial case is also clearer than ever. Businesses that invest proactively experience fewer disruptions and lower recovery costs, as outlined in Proactive Cybersecurity Return on Investment.
Stay Cybersecure in 2026
The cybersecurity landscape will continue to evolve. Businesses that treat security as a proactive, strategic function will outperform those that only respond to unfortunate incidents.
STACK Cybersecurity works with business owners and leaders to strengthen defenses, align security programs with real-world risk, and prepare for what comes next. Contact Us to discuss how your organization is approaching cybersecurity in 2026.
