IT Provider vs. Cybersecurity MSP
March 30, 2026
If your company handles sensitive data, operates under compliance requirements, or has experienced a security incident in the past few years, your current IT provider may no longer appropriate cybersecurity protections.
Traditional IT support focuses on uptime and help desk response. A cybersecurity-focused IT managed service provider (MSP) does something different: reducing the risk of a breach before one happens in addition to increasing uptime and providing top-notch help desk support
For manufacturers, legal and financial firms, that distinction matters more than ever. Regulatory frameworks like Cybersecurity Maturity Model Certification (CMMC), National Institutes of Standards and Technology (NIST), and SOC 2 Type 2 require structured security programs that most traditional IT providers can't deliver.
And when your company experiences a breach without proper controls in place, the financial consequences can easily exceed $100,000. And that's before factoring in legal costs, regulatory penalties, or the loss of customer trust.
5 Signs Your Current IT Provider Isn't Enough
Most companies don't outgrow their IT provider overnight. The gaps appear gradually, and by the time they become visible, real risk has already accumulated. These are the clearest warning signs.
No 24/7 security monitoring or real-time alerting. Hackers don't observe business hours. If your provider only monitors systems during the workday, threats can go undetected for hours or longer. Dwell time, how long an attacker operates undetected inside your environment, directly determines the severity of a breach.
Reactive support instead of proactive protection. Break-fix IT providers are designed to respond after something goes wrong. That model has an inherent structural problem: the provider has no financial incentive to prevent the problems you're paying them to fix.
No compliance guidance. Frameworks like CMMC, NIST, and SOC 2 require documented security programs, evidence of controls, and ongoing monitoring. If your IT provider cannot walk you through a compliance audit, you're likely not compliant.
No strategic security leadership. Smaller companies rarely need a full-time Chief Information Security Officer, but they do need someone in that role. A cybersecurity MSP typically offers vCISO services, giving you senior-level security strategy without the full-time salary.
Offshore or outsourced support teams. When your data is in the hands of overseas contractors, accountability and response speed both suffer. For defense contractors and companies subject to federal compliance requirements, offshore support can also create legal and regulatory exposure.
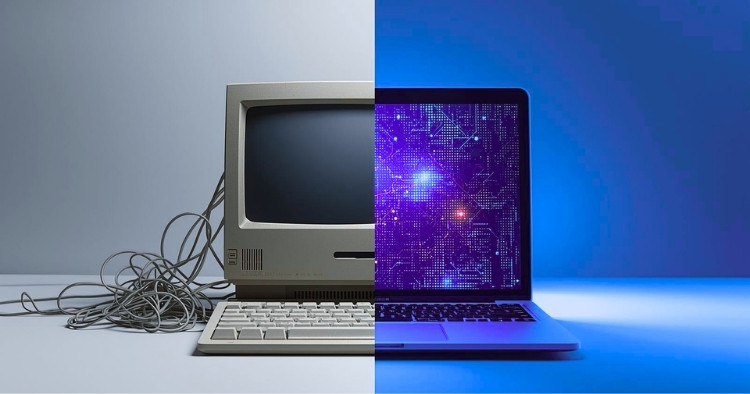
IT Support vs. Cybersecurity MSP
The differences aren't subtle. Traditional IT providers and cybersecurity-focused MSPs are built for different purposes, and the gap between them becomes clear when something goes wrong.
| Category | Traditional IT Provider | Cybersecurity MSP |
|---|---|---|
| Focus | Helpdesk, uptime | Risk reduction, threat prevention |
| Monitoring | Limited | 24/7 SOC with real-time alerting |
| Incident Response | Hours to days | Escalation initiated within minutes for active threats |
| Compliance Support | Minimal | Built-in frameworks (CMMC, NIST, SOC 2) |
| Security Strategy | None | vCISO included |
| Staffing | Often outsourced | 100% U.S.-based, no offshore teams |
At STACK, we operate under defined service level agreements (SLAs) for both help desk and incident response, and we consistently meet those targets. For active threats, response is initiated within minutes, not hours, and clients define in advance how and when they want to be contacted, including nights, weekends, and holidays.
Why Cyber Insurance Forcing Companies to Upgrade
Cyber insurers have fundamentally changed their underwriting standards. Companies that can't demonstrate specific technical controls are now routinely denied coverage. Or they face steep premium increases when they renew.
According to Coalition's 2024 Cyber Threat Index, 82% of denied claims involved companies that lacked multi-factor authentication (MFA). Marsh McLennan's research found that 41% of cybersecurity liability insurance applications are denied on first submission, with missing MFA and inadequate endpoint protection as the two most common reasons. These case examples represent a broad shift in how insurers assess risk.
What underwriters now require before issuing or renewing a policy typically includes endpoint detection and response (EDR), MFA across all users and systems, email security and phishing protection, tested backup and disaster recovery (BCDR), security awareness training, vulnerability management, and a documented incident response plan. Having a policy doesn't guarantee a payout if those controls weren't fully executed at the time of a breach.
A cybersecurity MSP helps you qualify before you apply. That means implementing required controls, maintaining documentation for underwriting, and keeping security posture consistent over time.
What You Gain by Switching
The case for a cybersecurity-focused MSP is about what a mature security program enables your business to do.
Faster threat detection and response. Real-time alerting and defined escalation procedures reduce attacker dwell time, which is the period during which a hacker operates undetected. Every hour of dwell time increases the scope and cost of a breach.
Compliance readiness. Structured frameworks and documented controls mean you're ready for audits and certifications.
Predictable cost. Bundled managed security services replace unpredictable incident response costs. Instead of paying emergency rates after something breaks, you pay a consistent monthly fee for proactive protection.
After-hours coverage. Threats don't stop when your office closes. A 24/7 security operations center (SOC) means your environment is monitored around the clock, with escalation protocols you define in advance.
What's Included, Why It Costs What It Does
Cybersecurity services for companies with 25 to 300 employees typically range from $150 to $400 per user per month, depending on compliance requirements, risk profile, and the scope of services included. That range reflects what a full-stack security program actually costs when built from components. Purchased separately, those components often exceed the bundled price.
Bundling these into a single managed service offering reduces complexity, removes coverage gaps, and gives you a consistent monthly cost instead of a collection of point solutions that may or may not work together.
Representative Scenario: Michigan Manufacturer
Consider a typical scenario for a Michigan-based manufacturer with around 85 employees that has been relying on a traditional IT provider for several years. When that company transitions to a cybersecurity-focused MSP, the first 90 days often reveal how significant the gap was.
Common findings include dozens of unpatched critical vulnerabilities, alert response times measured in hours rather than minutes, and no documentation that would support a compliance audit. Within the same period, a structured transition typically brings real-time escalation, CMMC-aligned controls across endpoints and network infrastructure, and internal audit readiness for the first time.
The cost of that transition is almost always less than the cost of discovering those gaps after a breach.
When Cybersecurity MSP Not a Fit
This type of service is not the right fit for every company. If your business has fewer than 10 employees, operates with minimal sensitive data, and has no regulatory requirements, a traditional IT provider or break-fix model may serve your needs at a lower cost.
The calculus changes as soon as compliance requirements enter the picture. If you handle controlled unclassified information, process financial data, store patient records, or work in a regulated supply chain, the risks of under-resourced IT support are not hypothetical — they are quantifiable and growing.
How the Transition Works
A well-managed transition to a cybersecurity MSP follows a structured process. It begins with a security assessment to identify current gaps, followed by a risk and compliance review. Migration planning covers tools, users, and systems. Parallel onboarding allows both environments to run simultaneously to avoid downtime. Once the transition is complete, continuous monitoring takes over.
The goal is to close the security gaps that currently exist, often invisibly, in the environment you already have.
Why Companies Choose STACK
STACK Cybersecurity is a Michigan-based, family-owned managed security service provider with more than 20 years in business. We use a 24/7 security operations center with 100% U.S.-based staff. We don't outsource or offshore support teams. We launched Michigan's first U.S. Department of Labor-certified cybersecurity apprenticeship. We're regularly featured on 92.7 FM The Answer in both Chicago and Detroit in addition to the cybersecurity education we offer on Channel 4 ClickOnDetroit. Our Chief Impact Officer, Tracey Birkenhauer, is the lead technology writer for Corp! Magazine. See our Press page. And check out our Awards
If your current IT provider is focused on keeping the lights on rather than keeping your data safe, it may be time for a more honest conversation about what your business actually needs. Contact STACK to start with a cybersecurity risk assessment CSRA.
Related Resources
- Cyber insurance requirements and risks
- Incident response best practices
- Multi-factor authentication explained
- Cybersecurity return on investment
- CMMC compliance overview
- Safeguarding manufacturing operations
