Boss Gift Card Scams Target Business
Mar. 6, 2026
Ruth had only been at the company for three days when the text arrived.
“Hi Ruth, this is Damian. Are you available?”
Damian was the company’s CEO. The message felt routine. Ruth replied.
A few minutes later, another message appeared.
“I’m in meetings all day and can’t take calls. I need your help purchasing a few gift cards for a client appreciation event. I’ll reimburse you later.”
Ruth wanted to help. The request seemed urgent.
Within minutes, the scammer asked Ruth to send the gift card codes. Fortunately, Ruth paused and checked with a coworker before acting.
Not every employee does.
Personal Information Exposure
Boss gift card scams are ridiculously common right now, especially when a new staffer doesn’t yet know communication norms. Scammers scrape LinkedIn or company websites, impersonate leadership, and pressure the employee to buy gift cards “for clients” or “for a surprise.”
This con is centered on social engineering, leveraging publicly available information and human psychology.
Most employees don’t realize how exposed their mobile numbers are. Companies such as ZoomInfo, Apollo, and RocketReach collect employee data from LinkedIn, scraped resumes, and breached data. Criminals buy or scrape this information to engage in smishing schemes.
Smishing, derived from Short Message Service "(SMS)" and "phishing," is a type of cybercrime using deceptive text messages to steal from victims.
Sites like Whitepages, Spokeo, and BeenVerified list personal information gathered from public records, including phone numbers, addresses, relatives, and emails.
If an employee used their personal phone number on a job application, conference registration, or LinkedIn, that number likely exists in breach databases.
“If I run a dark web scan on your email address, it’s nearly certain I’ll see it listed in a data breach,” said Rich Miller, CEO of STACK Cybersecurity.
Passwords Matter
Password hygiene matters in gift card schemes even when the scam arrives by text message. The credibility of smishing attacks often depends on information obtained from prior credential exposure. Login credentials are vulnerable for users who employ short, weak, easily guessed, and reused passwords.
Hackers rely on poor password hygiene to carry out crimes. They also appreciate users who save passwords in browsers.
While gift card scams delivered via text don’t require criminals to log into an employee’s email account, they frequently rely on data harvested from breached accounts elsewhere. They purchase breached credentials, including reused passwords, contact lists, calendars, and personal details, to convincingly impersonate executives or coworkers.
Remove Passwords Saved in Browsers
Saving passwords in your browser may feel convenient, but it introduces real security risk. Browsers are frequent targets for thieves. If your browser gets compromised, stored credentials can be extracted quickly. Anyone with physical access to your device may also be able to view saved passwords, putting multiple accounts at risk.
Refer to our blog, How to Remove Browser Passwords, for instructions to remove credentials from Chrome, Edge, Safari, Firefox, and DuckDuckGo.
STACK Cybersecurity offers live sessions to onboard clients to Keeper password manager. We help clients set it up, port over and delete passwords from browsers, as this is a significant cybersecurity issue.
Infostealer attacks surged 800% in the first half of 2025 alone. These malware programs target one thing: credentials stored in browsers. They harvest passwords, session cookies, autofill data, and authentication tokens, then disappear before most security tools detect them. Learn more from our post, Browser Passwords Remain Hacker Favorite.
Targeting People, Not Systems
Many companies invest heavily in firewalls, endpoint protection, and email filtering. Yet this scam bypasses those defenses entirely.
Instead of hacking networks, criminals impersonate executives and manipulate employees into transferring money.
It usually begins with:
- a text message
- an email
- a phone call
- or a social media message
Instead of exploiting software vulnerabilities, these schemers exploit corporate trust. Even high-tech companies like STACK Cybersecurity have received these nefarious text messages. Because they target people, not systems.
“These scams don’t break into networks or bypass security tools,” Miller said. “They impersonate trusted people and contact employees directly through their personal phones. That’s why, in these cases, awareness is even more important than mobile device management.”
Mobile device management, or MDM, primarily secures corporate data rather than blocking texting schemes. MDM acts more on app management and device security configuration rather than filtering text messages.
“Modern cybercrime is often about manipulating people, not hacking computers,” Miller said. “You can have the best cybersecurity tools in the world, but if someone impersonates your boss over text, technology may never see that message.”
Miller offers the following advice:
- No legitimate company will ask you to buy gift cards over text.
- If a message claims to be your boss but refuses a phone call, it’s suspicious.
- Always verify financial requests through a known contact method.
- Adopt a passcode with your family and employer.
Technically Legitimate Texts
Companies with strongest cybersecurity defenses may not detect this type of attack because the messages themselves are technically legitimate. Traditional security tools are designed to identify threats like malicious links, phishing emails, malware, or suspicious network activity.
In a boss impersonation scam, none of those indicators may be present.
The message often arrives as a simple text sent directly to an employee’s personal phone number, outside the company’s email system and security monitoring tools. Unlike phishing emails, which can be filtered using domain authentication, spam detection, and link analysis, SMS messages are far harder to screen or verify.
As a result, even the most advanced cybersecurity systems cannot reliably flag these messages. The attack succeeds not by exploiting a software vulnerability, but by exploiting trust and human behavior. That is, scammers target the human layer of cybersecurity. This is why cybersecurity awareness training is vital for every company of every size in every vertical and in every location.
What the Scam Looks Like
These schemes follow a predictable pattern. Example text conversation:
Scammer: “Hi Ruth, this is Damian. Are you available?”
Ruth: “Yes, how can I help?”
Scammer: “I’m tied up in meetings today and can’t take calls. I need your help quickly. Can you purchase a few gift cards for a client?”
Ruth: “Sure, what kind?”
Scammer: “Apple or Target cards. Send me the codes once you scratch them.”
The email version looks similar. Example email:
Subject: Quick favor
Hi Ruth,
I'm currently in meetings and need your assistance quickly. Please purchase a few Apple gift cards for a client and send me the codes once you have them.
I will reimburse you later.
Thanks,
Damian
Why Gift Cards?
Gift cards are appealing because they can be purchased quickly, are easily transferable, and become challenging to trace once the code is disclosed. These traits have made gift cards the top payment method demanded by fraudsters across all fraud categories, according to the Federal Trade Commission (FTC).
After the victim provides the code from the back of the gift card, the associated funds are typically redeemed within minutes.
The FTC offers salient advice: “Gift cards are for gifts. Only gifts. Not for payments. Never buy a gift card because someone tells you to buy one and give them the numbers.”
A Better Bet
Mobile phone users nearly always open text messages. In fact, text message open rates are as high as 98%, and response rates as high as 45%. Compare this to email open and response rates of 20% and 6%, respectively. With more than half of Americans texting daily, texting is the most common communication method today.
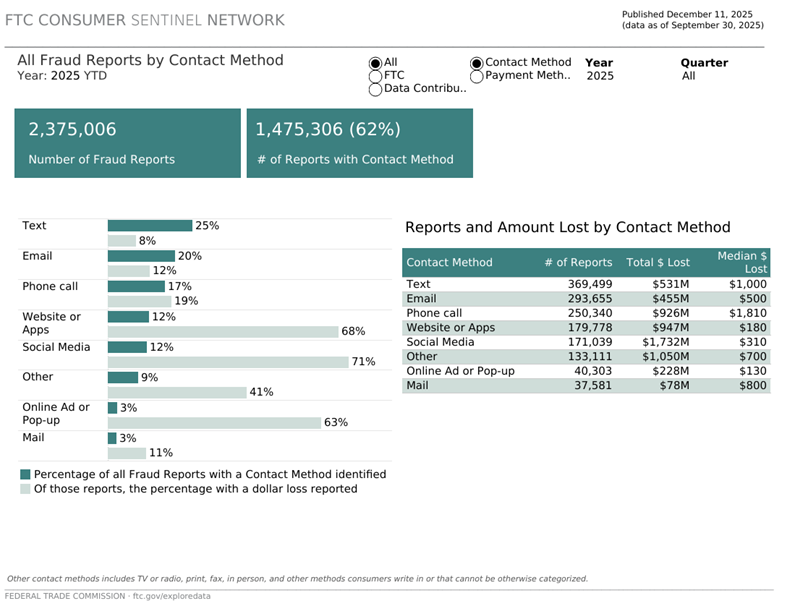
According to the FTC, text messaging is the most common method scammers use to reach victims, driving hundreds of millions of dollars in losses in 2025 alone.
How Rampant Is This Problem?
Gift card fraud is no longer fringe. The FTC reports hundreds of millions of dollars are lost annually to gift card scams alone. The hottest brands include Apple, Google, Amazon, Target, and Steam. Small and mid-size businesses are disproportionately targeted.
Scammers now specify exact gift card brand and dollar amount.
The Federal Trade Commission (FTC) issued a consumer alert on Jan. 28, 2026 titled “No, that’s not your boss asking you to buy gift cards."
The FBI reports that gift card requests are now a common Business Email Compromise (BEC) variant, including text requests sent to employees’ personal phones. BEC is the highest-loss cybercrime category, with billions lost annually. Gift cards have replaced bank transfers and wires in many scenarios, especially those involving employees. Fund wires and transfers remain dominant for high‑dollar fraud.
Criminals choose payment types based on speed, irreversibility, and victim profile, according to AARP.
The FTC puts it plainly: “Anyone who tells you to pay with a gift card is a scammer.”
Why Schemers Use Text Messages
Text messaging has become a preferred delivery method for scammers. Smishing is phishing, but through text messages.
“Smishing messages are sneaky,” according to the National Cybersecurity Alliance (NCA). “They often disguise themselves as urgent alerts from banks, delivery services, government agencies, or even your boss. The goal is always the same: get you to act quickly before you think hard about the request.”
Smishing messages are more difficult to verify than email and take advantage of the personal nature of mobile devices. SMS messages also have extremely high open rates compared to email, which makes them attractive for attackers trying to reach employees quickly.
SMS scams rely on convincing staff that urgent action is required to avert a threat or secure a benefit. The urgency is an essential aspect.
New Staff Targeted
Hackers frequently identify potential victims through public sources like LinkedIn.
Posts announcing a new job can signal that someone:
- may not yet know company policies
- wants to be helpful and responsive
- may feel pressure to assist leadership
New employees therefore become attractive targets for impersonation scams.
Employ a Corporate Password
Some companies are introducing a concept called a corporate password.
This is a shared verification phrase used to confirm sensitive requests within a company.
If someone claiming to be a manager asks an employee to make a financial purchase, the employee can respond like this:
"Before I proceed, what's the corporate verification phrase?"
If the sender can't provide the phrase, the request should be verified through another channel. Because scammers rely on impersonation and urgency, this simple step can immediately disrupt the attack.
Red Flags
Employees should pause if a message includes any of these warning signs:
- The sender claims to be an executive
- The request involves gift cards or urgent purchases
- The sender says they can’t take a call
- The employee is asked to send gift card codes or receipts
- The message pressures the employee to act immediately
How to Respond to Smishing
If an employee receives a suspicious request:
- Verify through another channel. Call the person directly using a known company phone number.
- Don't send gift card codes. Once the codes are shared, the funds are usually gone.
- Report the message internally. Notify your IT or security team so other employees can be warned.
Where to Report Gift Card Scams
Reporting incidents helps investigators track criminal campaigns and warn other potential victims.
Federal Trade Commission (FTC)
FBI Internet Crime Complaint Center (IC3)
If the cards were purchased in-store, contact the retailer’s fraud department.
Pause, Verify
Modern cybercrime increasingly targets people rather than systems. When someone asks for money, purchases, or gift cards, pause and verify the request. Or, as AARP suggests: Pause. Reflect. Protect.
“We see some form of the active pause in high-pressure fields like aviation, emergency medicine and military operations,” according to AARP. “Now we can apply it to the high-pressure situation of a fraud attempt.”
Gift cards are attractive to criminals because they’re fast, irreversible, and bypass traditional financial controls, making them ideal for lower dollar, high volume attacks delivered via email or text. The result is a two-track fraud model: wires for scale and dollar value, gift cards for speed and success, underscoring why technical controls alone are insufficient without employee training, verification policies, and mobile-aware security practices.
Ready to Get Cyber Secure?
Related Resources
Scammers Preferred Payment Method
Association for Financial Professionals (AFP)
Verizon 2025 Data Breach Investigations Report
No, that's not your boss asking you to buy gift cards
